P2SH or Pay-to-Script-Hash addresses are a special type of address in Bitcoin, which allows you to create addresses that can receive or send transactions in which a series of instructions must be followed in order to unlock the balances that contain those addresses.
El Pay-to-ScriptHash, or also known as P2SH, is a script format used on the network Bitcoin which allows you to lock the bitcoins in the script hash (one part) and then provide the original script (full) when the bitcoins are unlocked at the time of transaction.
This feature makes it possible to create custom redemption scripts that can be easily shared with other users. In other words, it allows you to create addresses or transactions with unconventional programming. And these can only be unlocked by fulfilling a series of pre-established conditions.
Since 2012, Bitcoin and other cryptocurrencies have incorporated the P2SH format in many of their addresses. Through which transactions can be sent to a script hash, instead of a public key hash. That is, transactions are sent to an address that begins with 3 instead of one that begins with 1 (ECDSA). So that addresses encoded in this format represent the encoded hash of a script and not that of an ECDSA public key.
Likewise, due to this feature, P2SH format addresses are generally used to carry out transactions multi-signature addresses. Although this is not its only use. With P2SH you can configure addresses that can represent a script through which other types of transactions are encoded. For example, with P2SH a user can send their bitcoins to a secure address in many possible or unusual ways without being aware of how security has been configured. While the user receiving the transaction may need to meet certain conditions or special instructions in order to unlock the transaction.
Example of a P2SH transaction
A P2SH transaction works because the scriptPubKey contains a hash that must be unblocked in order to release the payment of the blocked bitcoins. First, the transaction unlock source script (redeem script or redemption script) is inside the transaction scriptSig.
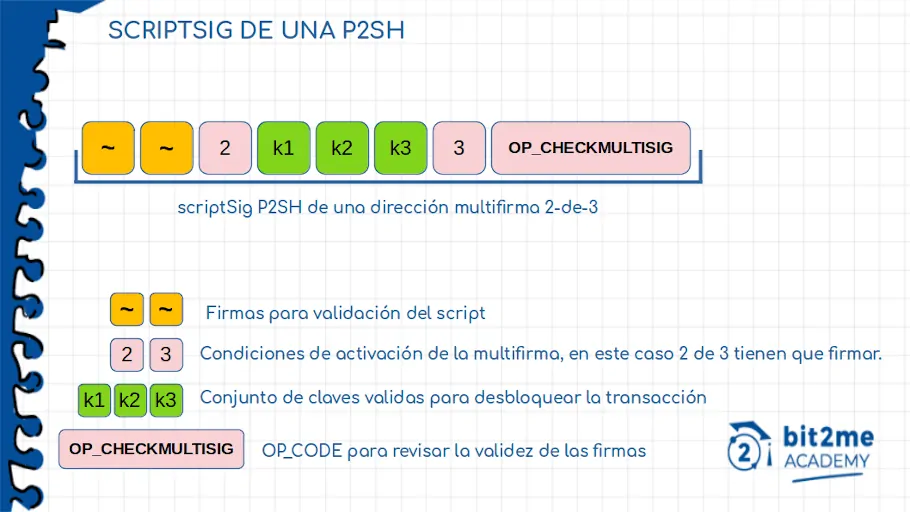
Here we can clearly see that the scriptSig makes mention of an address MuSig or multi-signature of the type (2 of 3). In it we see three keys (the keys in the image), two signatures (of the participants in the transaction) and the OP_CODE (opcode), OP_CHECKMULTISIG. What this part of the transaction script will do is verify that the signatures and keys within it are capable of unlocking the operation.
That is, verify that at least 2 of the three authorized people are making the transaction. Once the script has verified this, we can be sure that we have in our possession the bitcoin unlock script and we move on to the second part.
In the second part we see how the scriptPubKey of a P2SH transaction has the following structure:
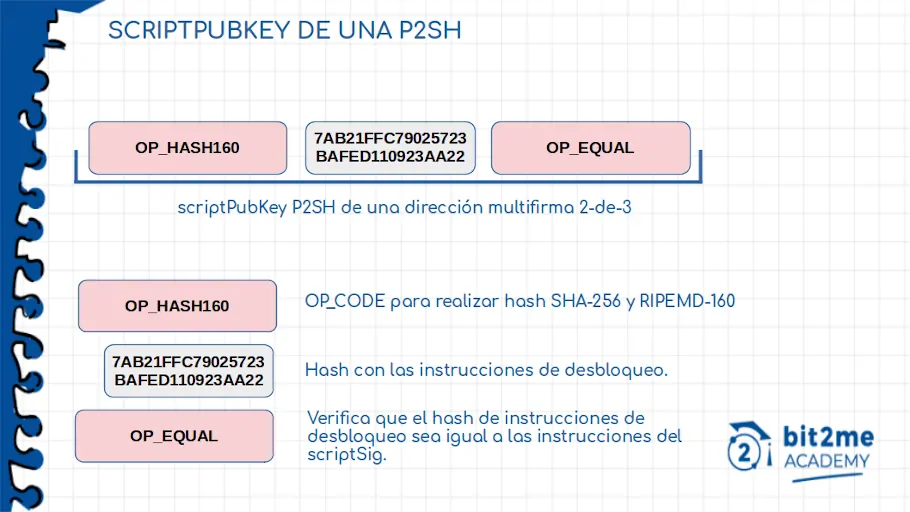
These OP_CODEs tell us that the scriptPubKey will only be unlocked if we can prove that we have the transaction origin script (the redeem script checked in the Sig script). For this we must take the result of this script and execute the operation OP_HASH160. In other words, apply a hash to the script SHA-256 and then a RIPEMD-160. The result will be compared to the “hash script” inside the scriptPubKey (this using OP_EQUAL) and if the result is identical, we will have successfully unlocked our bitcoins.
Implementation of the P2SH format in the Bitcoin addresses
BIP-0013
El Pay-to-ScriptHash address format was initially introduced in the 13 BIP designed by Gavin Andresen. Where it describes a new format for Bitcoin addresses with which complex arbitrary transactions can be supported.
In this BIP Andressen describes that this new format for Bitcoin addresses will use a fixed length of 20 bytes. Representing the hash of the script through which you can exchange cryptocurrencies. And that it can be easily used and scanned from a QR code, or quickly copied and pasted to carry out the desired transaction.
Likewise, Andresen describes that the function 4 is integrated in the first XNUMX bytes of the byte sequence. address checksum or checksum, which strengthens the infrastructure and security of the Bitcoin network. By allowing the implementation of a much more secure, optimal and efficient verification method than simply truncating SHA-256. At the same time, an own identity is added for each address created in the network.
BIP-0016
Likewise, in the 16 BIP, which was announced a few months after BIP 13 by Gavin Andressen, P2SH is explained as a soft fork to the Bitcoin protocol designed in a way that allows P2SH addresses to be established as a new type of standard transaction. That seeks simplification in the use of scripts in any type of transaction, however complex it may be.
BIP 16, along with BIP 13, aims to minimize the changes that need to be made to the supporting infrastructure of the Bitcoin network. Making it easier to be able to share blocking scripts with other users, no matter how complex these scripts are.
For example, before the implementation of P2SH if you wanted to add a complex blocking script to your bitcoins, you needed to share the entire blocking script with the user who carried you over. But with the arrival of P2SH it is now possible to give that user only a part of the blocking script, instead of the entire sequence. That is, only one hash of the script can be delivered instead of the entire script.
Advantages of implementing P2SH
Multi-signature addresses
P2SH activation gives you allows users of the Bitcoin system to carry out or receive transactions in multi-signature addresses. In fact, this is the most common application known for the P2SH format. Because P2SH-formatted addresses are designed to support a set of signatures that is equal to or less than the number of private keys that are linked to or associated with them. That is, in a multi-signature address that has 3 associated keys, the 3 keys can be the signatories, or failing that only 2 or 1 of them.
Moreover, Bitcoin addresses that use the P2SH format are easily identified as they start with number 3. But even though it's often used to create multi-signature addresses, it doesn't always mean that an address starts with this number that it is a multi-signature address. An address starting with number 3 will always be a P2SH address, but it will not always be a multi-signature address.
Security and Privacy
Through the P2SH format a user can finance any script without knowing what are the spending conditions that are linked to that script. In other words, the user can send or share the scripts associated with a transaction without having partial or total knowledge about the configuration of these conditions or security instructions.
Therefore, in the case of being a sender, the user will only have to send the transactions they wish to carry out to the P2SH address. No need to know how the funds you have sent will be spent. While in the case of being a recipient or recipient, the user must know the conditions of expenses associated with that transaction. That can vary between the need for a multi-signature, password or another, to be able to access the cryptocurrencies that have been sent to you.
Likewise, if the P2SH blocking script only contains one hash of the script, it is impossible to know what type of script comes from that hash. Making it impossible for a user to know if a transaction comes from a particular address or a multi-signature.
Smaller unspent outlets
Like all unspent outlets or utxos Bitcoin are stored in the RAM of the nodes, it is important to save this storage space. Thus, by employing P2SH blocking scripts with smaller sequences, the UTXOs will require less space to be stored, allowing the nodes to be computationally more efficient and to work in an agile and competent way in the validation of network transactions.
Lower commission rates
Since the commission rates that are charged in Bitcoin are not related to the amounts transferred but to the size of the transactions, a script hash with a shorter length allows the sender of a transaction to be able to send their funds to P2SH addresses without having to have to pay high commission fees. As it would happen in the case of using the complete scripts.
Although this may not be a serious problem today, it may be in the future; when mining rewards are reduced and nodes are maintained at transaction commission rates.
followed
P2SH format addresses support both addresses followed as with those that are not. So users can easily send their funds and transact in both wallets.
Disadvantages of P2SH implementation
The truth is that P2SH has very few disadvantages or limitations. Because P2SH was implemented time after the development of the original Bitcoin scripts, so the developers had the opportunity to correct the limitations that were presented on the network at that time. However, the limitations of P2SH are:
Data size
P2SH takes up more space within the blockchain. This can lead to congestion and influence the network's operating capacity. This is because during the blocking of bitcoins in P2SH 25 more bytes are added to the original script, leaving a multi-signature 2 of 3 script that uses P2SH with 278 bytes. Compared to the 253 bytes that the same 2 of 3 multi-signature script would have using P2MS.


 Author
Author