Phala Network (PHA) is a project focused on offering a secure and private distributed computing platform, which uses the TEE available in many CPUs to achieve the construction of a blockchain network with advanced capabilities of smart contracts and privacy.
Ehe Phala project uses Polkadot's Substrate technology to build a blockchain platform of confidential smarts contracts, powered by a block production system that harnesses the potential of CPU and a set of specialized functions known as "Safe Enclaves". With this, Phala Network wants to offer its users confidential computing and data protection services.
Phala Network is currently built on Polkadot and seeks to get hold of one of the parachains available on this network. In addition, Phala has a Canarian network called Khala, which works on the network Kusama.

Phala Network Objective
The main objective of Phala Network is build a general-purpose smart contract platform that preserves the privacy and security of its users at all times.
For this, Phala Network promises features such as:
- Confidentiality. Unlike the existing blockchains for smart contracts, Phala Network seeks to avoid the leakage of any entry, exit or intermediate state of a confidential contract. It only answers the consultations authorized to the contract.
- Code integrity. Anyone can verify that an output is produced by a specific smart contract published on the blockchain.
- Consistency of state. Anyone can verify that an execution occurred at a height of the blockchain, which implies that the result of the execution is subject to a certain state of the chain.
- Availability. There should be no single point of failure, such as disconnecting the miner.
- Interoperability. Contracts can interoperate with each other and with external blockchains.
How does Phala work?
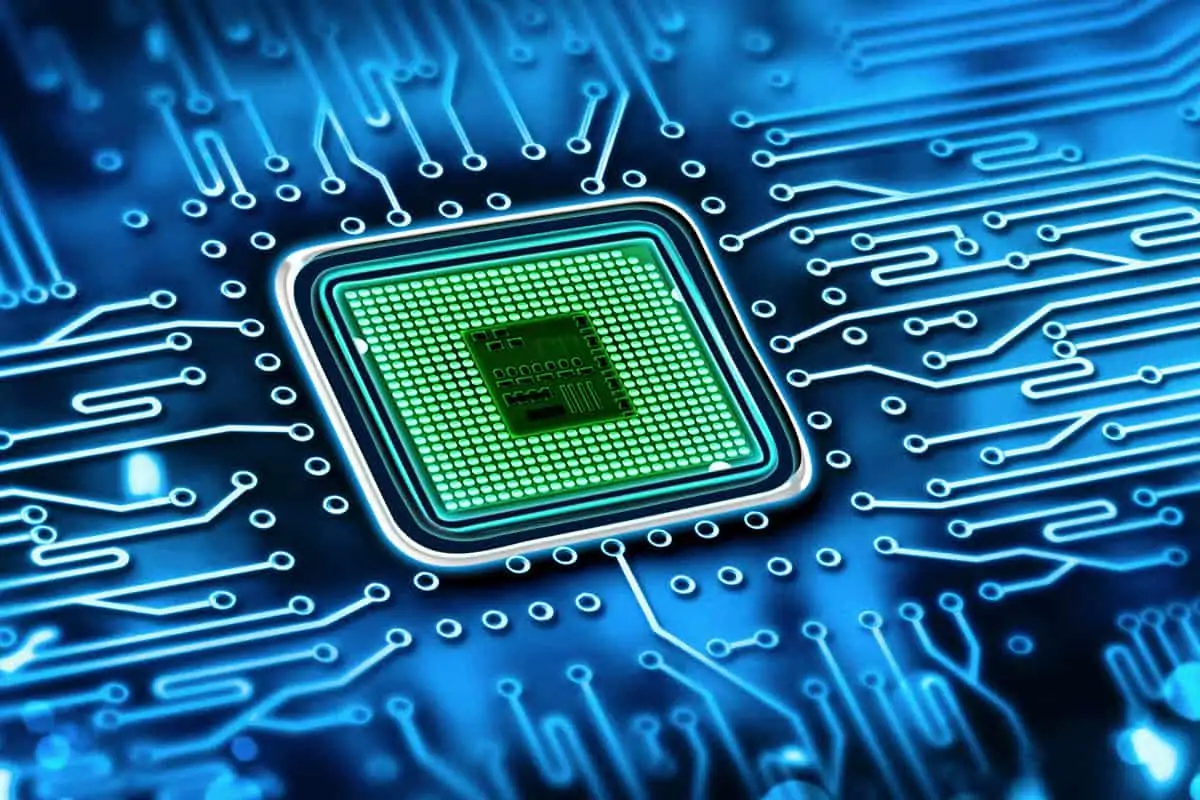
To achieve all this, Phala Network supports the operation of your network on TEE (Trusted Execution Environment or Trusted Execution Environment), which is nothing more than a special feature of the CPUs that we can find in our computers or smartphones.
For example, Intel CPUs have the Intel SGX solution, which allows us to enjoy a TEE integrated in said CPU. Other brands such as AMD also have this type of option (AMD SVE) and in ARM (smartphone CPU) we find options such as Trusted Zone.
In any case, this function allows Phala Network to create a secure execution environment for smart contracts, preventing the leakage of sensitive private information. To do this, Phala Network builds an entire blockchain network with the following roles.
Roles within the network
The Phala Network protocol is built on the following roles:
- Users. Users invoke, query and deploy smart contracts. Users interact with these smart contracts through the blockchain and worker nodes. They can verify the data on the blockchain, as well as the cryptographic evidence arranged in it by running a thin client or a full node. No special hardware is required for users to use confidential contracts, and this capability is available on virtually all current CPUs (from 2015 and later).
- Work nodes. Worker nodes execute confidential contracts on TEE-compliant hardware. These nodes work off-chain. At each node, a special program called pRuntime is deployed in the secure enclave (the secure part of the TEE). Worker nodes can in turn be divided into three functions:
- Genesis node. The Genesis Node helps boot up the network and set up cryptographic settings. There is only one Genesis Node and it is destroyed after the launch of the Red Phala.
- Gatekeepers. Gatekeepers manage secrets to ensure network availability and security. Gatekeepers are dynamically elected on the blockchain and need to perform staking within the network in order to be elected. Due to their homework, they are rewarded for being online and removed for bad behavior because there must be a certain number of functional Gatekeepers at any one time.
- Miners. The miners execute the confidential contracts. They are paid to provide their computing resources to users. Unlike gatekeepers, miners only need to stake a small amount of the Phala token and can enter and exit the network as they wish. In order to participate in PHA mining, it is necessary to stake 1.620 PHA tokens for each CPU core used in mining.
- Remote attestation service. It is a public service to validate if a worker Node has deployed the pRuntime correctly. In that case, the cryptographic evidence produced by the service can prove that a certain output is produced by pRuntime executed within a TEE.
- Blockchain. It is the backbone of the Phala Network. It stores the identities of the worker nodes, the smart contracts published, the status of the encrypted contracts, and the invocation transactions of the users and other blockchains. When connected to a Polkadot parachain slot, it is able to interoperate with other blockchains through the Polkadot relay chain.
PHA, the native token of Phala Network
The native token of the Phala Network platform is called PHA and it is a utility token that has different functions. Its main function is to reward the miners and gatekeepers of the network, since the operation and security of the network falls on them. The total supply is 1.000 billion tokens.
The departure of the PHA token was made through a private token sale at a price of $ 0,01 which was allocated 15% of the total PHA supply (150 million PHA tokens). Beyond that no ICOs took place, nor any other sale. Additionally, the Phala developers decided to release the tokens following the following distribution scheme:
- 5% of the total tokens are awarded to developers as a reward for the development of the protocol (50 million PHA tokens).
- 9% of the total tokens were allocated to an airdrop aimed at all those interested in the project (90 million PHA tokens).
- 1% of the total tokens were distributed to all network testers as a reward for their work and feedback in development (10 million PHA tokens).
This means that a total of 30% of the tokens have been distributed, leaving the remaining 70% for the reward system of the miners of the network (a total of 700 million PHA tokens).
Conclusions
Phala Network is a network focused on offering advanced private computing services supported by smart contracts deployed in Polkadot's parachains. Its curious operating system is reminiscent of the business protocol developed by the Linux Foundation, Hyperledger and its protocol Proof of Elapsed Time (PoET), which is widely used within private companies that offer BaaS services (Blockchain-as-a-Service or Blockchain as a service).
As a result, Phala Network is committed to a new security scheme that combines the power of blockchain and its proven robustness, with security systems embedded in hardware, in order to offer greater privacy to users.
However, Phala Network is a project still under construction with great possibilities, especially due to its commitment to private smart contracts, which can have a great impact for companies and services focused on security and respectful of regulations, such as the RGPD. of Europe. This makes it a project of great interest to both users and business services concerned about privacy.

 Author
Author