In computer security, the hash function is very important to guarantee the integrity of the transfer and registration of information that requires high levels of protection.
Hash functions are used in actions such as user validation and authentication, document signing, and also in cryptocurrencies, as a method to avoid counterfeiting of transactions and prevent malicious actions.
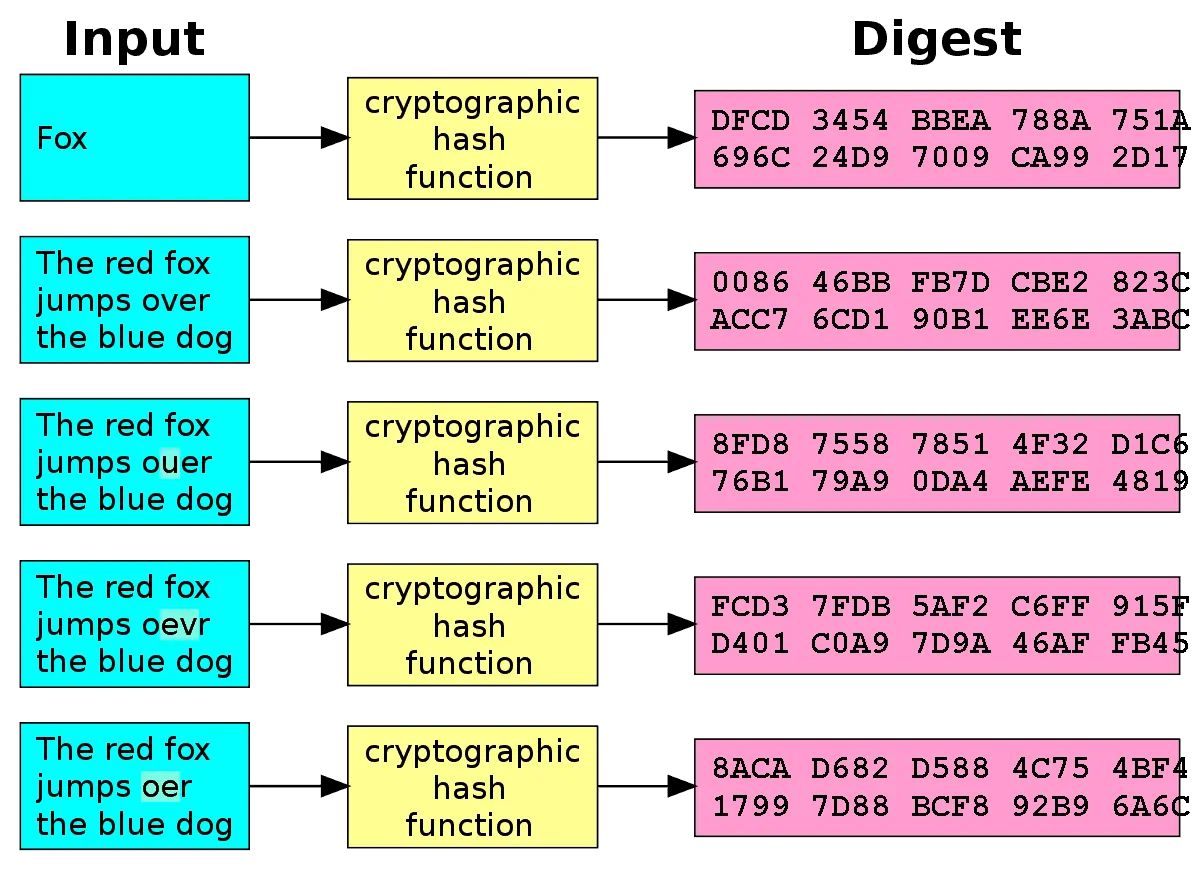
A hash function is a cryptographic procedure where a specific algorithm is used to transform specific information (for example, text) into a single fixed-length alphanumeric sequence, called a hash.
As we have already explained in detail what is a hash In the previous chapter, we will not go into much detail, but we will highlight that a hash does not come as a result of encryption, but rather that it is a one-way summary because the process is irreversible, that is, you cannot decrypt / retrieve the original information to Starting from the final hash if it is not trying to hash without stopping until you find the original text, since the hash found will match the one you were looking for and you already knew.
Over the years there have been many ways (algorithms) to generate hashes, that is, there are many types of hash functions, but dfrom a technical point of view, all must have a series of characteristics to fulfill their mission correctly:
- Unidirectionality: If we have an M document, the hash allows us to make a summary hash of it called h (M), but from this hash it is impossible to know the content of the original document M.
- Compression: The weight of the M document is irrelevant since the resulting hash will always have the same length with the same number of bits.
- Ease of calculation: It must be easy to calculate h (M) from 'M' for quick generation and without wasting time, energy and computing power.
- Bit broadcast: The hash h (M) must be a complex function of the original message 'M'. If it were the case that M was modified anywhere, and even if it were a minimal modification, the element h (M) would change completely.
- Weak collision resistance: It will be computationally impossible that known M, we can find another M 'such that h (M) = h (M'). First pre-image.
- Strong resistance to collisions: It must be computationally difficult to find a pair (M, M ') such that h (M) = h (M'). Second pre-image.
Hash security
Yes. You can find the original text of a hash. But it is practically impossible. Only by brute force.
For example, the 128-bit hash (a basic version of the hash) has 2 ^ 128 different possibilities and the 50% probability would be the square root of 2 ^ 128 which results in 2 ^ 64 being an instance. From this it is obtained that at a statistical level it is easier to break the collision than to break the resistance of the previous image.
So it is true, there is no hash function in the world that is free of collisions, but if it does not have a flaw in its design, getting it broken is very complicated and would take a significant time, sometimes billions of years with a capacity calculation higher than that of the entire planet earth.
Hash function in Bitcoin
One of the quintessential hash function algorithms is the SHA-256, it is used in countless cases due to its balance between security and generation complexity (in terms of time and energy expenditure)
One of the hundreds of thousands of places where it is used is in Bitcoin.
Within the Bitcoin ecosystem the function of the hash is very important as long as it is efficient, and for this to be the case, the hash must be complex, thus offering a high degree of security, which implies that more time is required for its calculation and the process is more inefficient.
The Hash function in Bitcoin is used in two areas.
1. Creation of the address
One of the most common uses of the hash function is in the process of generating the Bitcoin address.
The SHA256 hash function is used up to 3 times in the address generation process.
Thanks to this function, the address is shorter than the public key from which it comes. In addition, it is achieved that it is consistent as a whole when generating control characters (checksum).
If you still do not know how an address is generated, you can go by the following link.
2. Mining: Proof-of-Work
As we have already explained in detail in the chapter dedicated to bitcoin mining, is the action carried out by certain people who decide to offer their computing power to the Bitcoin network for the verification of different transactions.
Hashing is a key process in block creationWhat's more, it is also used in multiple steps, since the miner must associate the transactions with the block. To do this, use the hash function to create the Merkle tree.
With that result, in addition to the hash resulting from the previous block and a data that must be invented (called nuncio) must get the resulting hash to have a certain pattern. If you do, you will have solved the mathematical problem, you will have mined a block and you will win almost € 50.00 currently (June 2020).
This is how it is possible to completely link all new and past transactions, generating total integrity and immutability
Doing the hashing process once is extremely easy, but the miner must do it millions of times. It's like doing a squat, which is easy, but a million times not.
Finally, so that the nodes. Verify that everything is correct, they will do the process once, applying the hash function again in the different parts of the process.
Now you know what a hash function is and what roles it plays within cryptocurrencies. We encourage you to continue training to become an expert in cryptocurrencies and blockchain technology.




 Author
Author